Windows DCOM Hardening And OPC Classic Applications
Introduction
Microsoft has identified security issues within Windows operating systems and they have been applying a few hardening changes in the latest updates. After March 14, 2023 the hardenings will be effective in all updated Windows computers and this may affect your OPC Classic applications.
The main hardening is applied to computers that are running OPC Classic Servers. After the hardening, OPC Classic Client applications will not be able to connect over the network to OPC Classic Servers without additional measures to be taken.
I wrote a more technical article about the updates last year. Check it out if you want to learn which applications are affected and how to update them or how to update your own applications built with Prosys Sentrol OPC UA & Classic SDK for Delphi.
Terminology
To keep the definitions clear I will use the following terms:
- OPC Classic Server = the DCOM based OPC DA, AE or HDA server application that is running on Windows
- OPC Classic Client = the DCOM based OPC DA, AE or HDA client application that is running on Windows
- Server Computer = The computer on which the OPC Classic Server is running
- Client Computer = The computer on which the OPC Classic Client is running
Also I will use the terms:
- Unhardened = computer that has NOT been updated
- Hardened = computer that has been updated
The updates have been running over a migration period, but since this period will be over in March 14, 2023, I will assume that the hardenings are effective with the updates.
Definitions
Hardened Server Computer
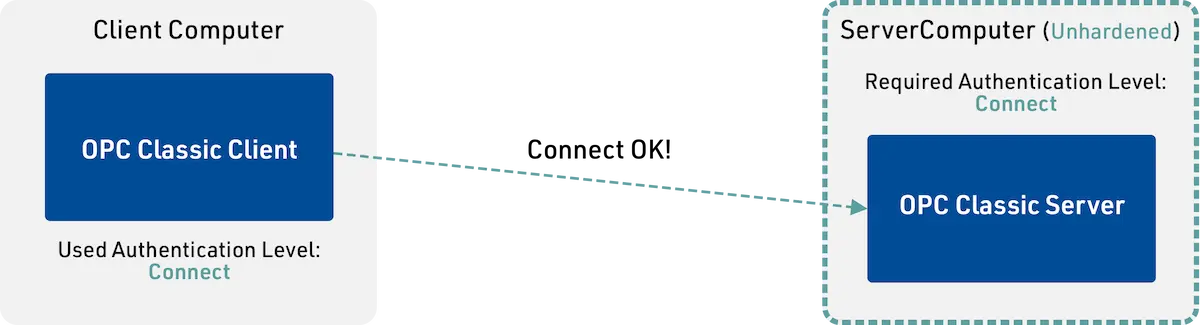
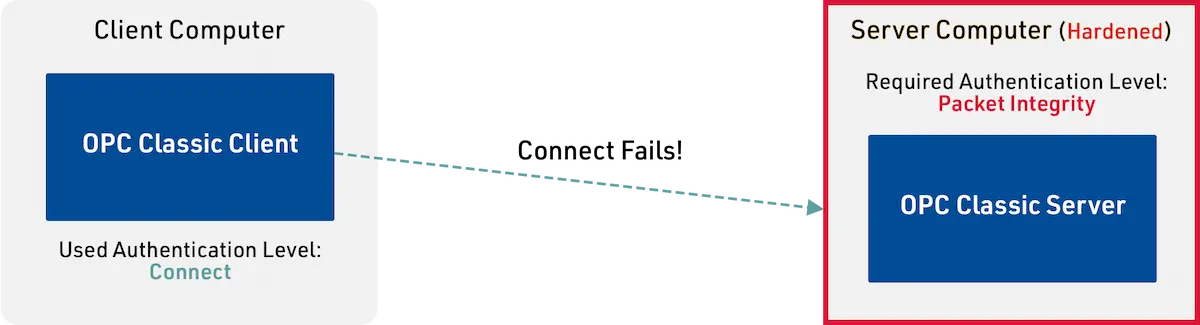
The hardening that is applied to the Server Computer will raise the required Authentication Level from Connect to Packet Integrity. This will disable OPC Classic Clients from connecting, unless they use the new Authentication Level.
Hardened Client Computer
The hardening will make the operating system to raise the used Authentication Level in non-anonymous connections to Packet Integrity, even if the application would use Connect.
Alternative Strategies
With these definitions your alternatives to ensure that your connections will continue to run smoothly are:
1. No updates – Unhardened Server
If you don’t update the Windows at your Server Computer, the OPC connections will not be affected. If you don’t apply updates published after June 7, 2021, nothing is changed. If you don’t apply updates after March 13, 2023, you can still disable the hardening. However, since this is an security improvement, you should not skip the updates because of this.
2. Hardened Server – Updated OPC Classic Client
If only the Server Computer is updated, the OPC Classic Client will not be able to connect by default, since they are typically using the Connect Authentication Level.
If the OPC Classic Client is updated to use the Packet Integrity Authentication Level, then it can connect again.
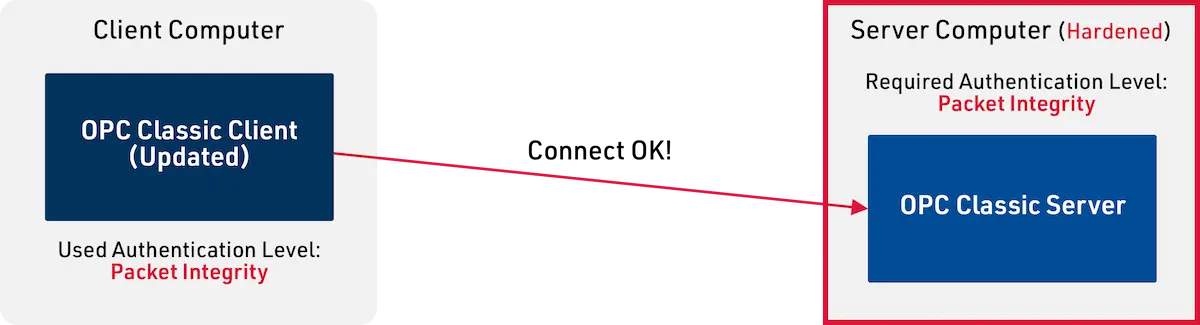
Check your vendor, if they have an update available.
3. Hardened Server & Client Computer
If you apply the latest Windows updates both to your Server Computer and Client Computer, the connections should run smoothly, since the client update will raise the used Authentication Level to Packet Integrity, even if the applications are not updated.
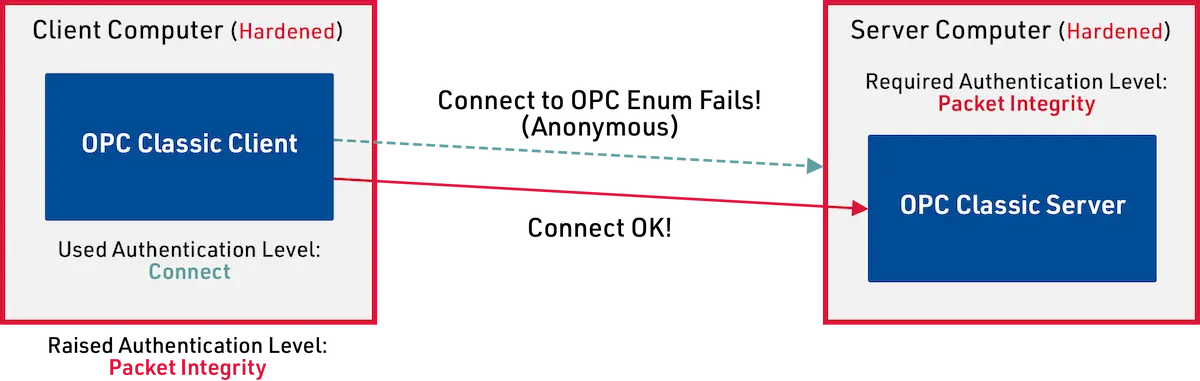
However, there might be some functionality in the OPC Classic Client that does not work properly any more. Namely, the OPC Enum service that is used to access the list of available OPC servers may not be available, and this may affect the client’s ability to connect to the server, after all.
4. Use OPC UA
Your best option and the most future-proof alternative in any case is to move from OPC Classic to OPC UA. In this case, you can disable DCOM and be sure that DCOM issues will not affect you anymore.
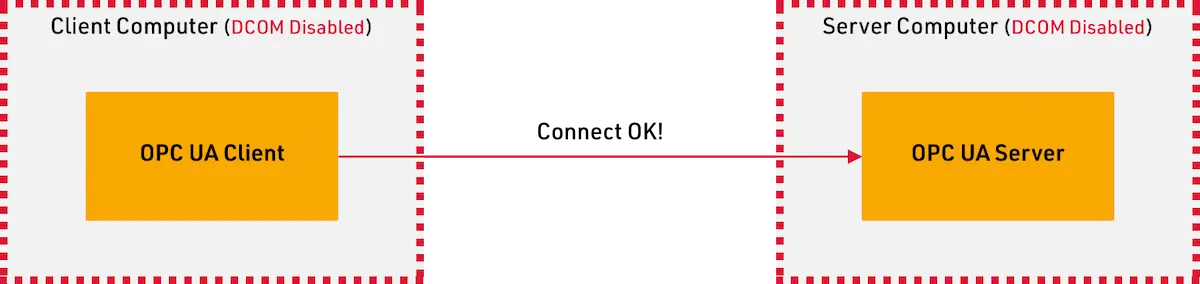
OPC UA is a full replacement to OPC Classic and the best option is to update the OPC applications to use OPC UA instead of OPC Classic. If that is not possible, you can use UaGateway to convert OPC Classic communication to OPC UA. You should do the conversion in the Client and Server computers, in which case no DCOM communication is required and you can disable it completely in the operating systems.
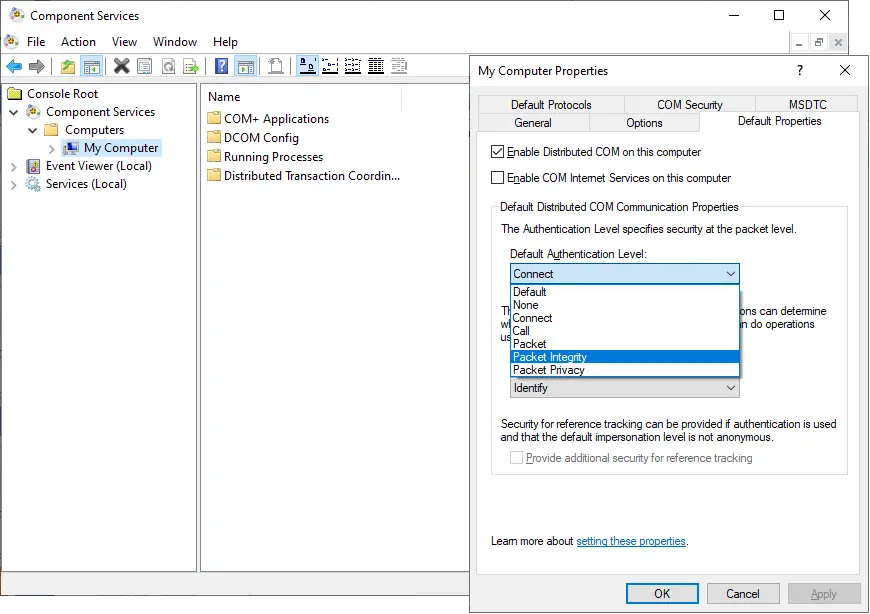
DCOM Configuration
You can configure the DCOM settings with dcomcnfg.exe. In practice, you will be taken to the Component Services application. If you find My Computer from the tree view and open Properties from the context menu, you will find DCOM settings from the Default Properties page. The Default Authentication Level is applied to all DCOM servers by default. This may not play a big role in future anymore, since you cannot really use any lower levels anyway.
More Information
We at Prosys OPC are experts in OT/IT integration. Our products, solutions and expertise help our customers convert their production processes to be ready for Industry 4.0 migrations. Additionally, we are a reliable partner for both analytics companies, factories and plants. Don’t hesitate to contact us by email at sales@prosysopc.com or through our website contact form.
Author Info

Jouni Aro
Chief Technology Officer
Email: jouni.aro@prosysopc.com
