Securing Industrial Networks for NIS2: How Prosys OPC UA Forge Solves the Connectivity
Industrial cybersecurity is shifting from “best practice” recommendations to a legal framework that companies with critical infrastructure and production operations must follow. Especially, the EU’s Network and Information Security Directive 2 (NIS2) introduces a set of security requirements that organizations cannot overlook and are forced to act in an industrial world where quarters last 25 years, within a very short time period.
For most industrial companies, the primary problem in meeting the requirements isn’t understanding the directive, but implementing the technical architecture required to meet it for old brownfield environments.
What is NIS2 and Who Is Affected?
NIS2 applies to both Essential and Important entities, based on their number of employees or yearly turnover. In addition to traditional critical infrastructure (energy, water, transport), it covers a broad range of companies in manufacturing sectors such as:
- Food & Beverage
- Chemicals
- Electronics
- Machinery
- Pharma & Medical
- Transport Equipment
As with any EU directive, the actual legislation is made by the member states, and the deadline for this was October 2024. In 2026, the enforcement period begins, and companies and organizations must demonstrate their risk management and security measures.
The Core Requirement of NIS2 is to adopt a risk-based model (Article 21), requiring organizations to implement measures to prevent, detect, and respond to incidents. In OT environments, this means the companies need to implement network segmentation, secure communication, and strict access control.
Where Prosys OPC UA Forge Fits In
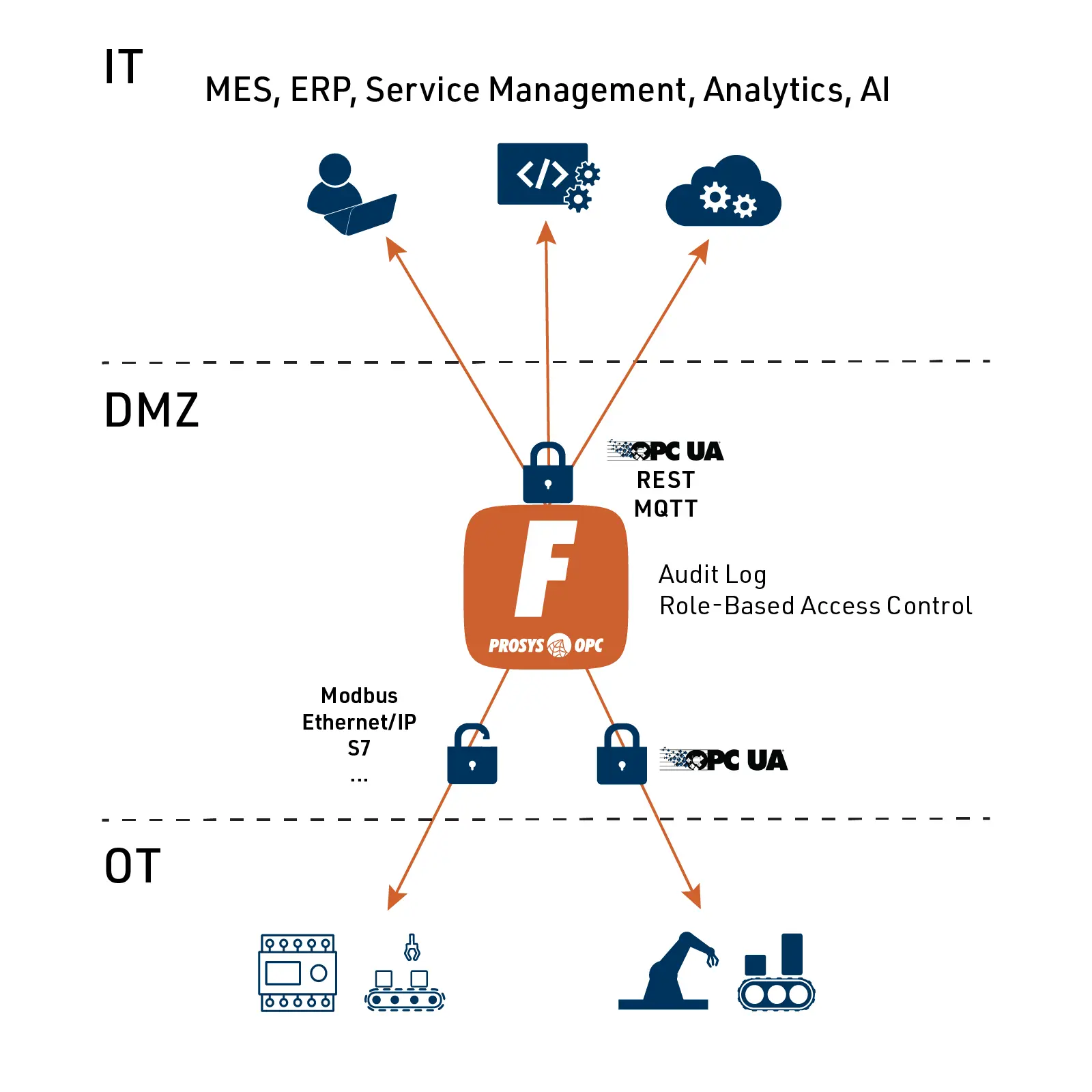
NIS2 covers everything from governance to incident reporting. Prosys OPC UA Forge is not a silver-bullet solution for the entire directive, but it solves the most difficult technical challenge: secure data exchange between OT and IT networks.
While NIS2 strongly promotes the use of cryptography and secure authentication, all industrial protocols, with very few exceptions, transmit data in plain text without any security.
Prosys OPC UA Forge acts as a secure integration layer. It connects to legacy devices using their native protocols and converts that data into OPC UA. OPC UA enables a lot of security enhancements over the legacy protocols, such as:
- Encrypted communication
- Message signing and application authentication
- Certificate-based trust management
- Role-Based Access Control
- Audit logging
- + many other security features
By using Forge together with network segmentation, all data leaving the OT network is fully secured and authenticated, meeting the NIS2 requirements for data integrity.
The Full NIS2 Checklist
While Forge secures data transfer, total compliance requires further organizational steps. Organizations must also address:
- Secure Remote Access: Using, for example, IT-managed engineering jump stations for any engineering and maintenance work done for the OT resources.
- Incident Response: NIS2 requires that “Significant Incidents” are reported within 24 hours. This requires internal processes for detecting and escalating security events.
- Supply Chain Security: Organizations need to assess the security posture of their software and hardware vendors and integrate them as part of risk management.
- Cyber Hygiene: Having clear best practise processes for basic security policies such as password policies, patch management, and staff training.
Conclusion
NIS2 is a significant change in industrial security for many companies involved, but fortunately, there are good tools available to implement policies and technical architectures that make commissioning easier.
Using Prosys OPC UA Forge, our Industrial DataOps platform, as a security gateway, you can drastically reduce your attack surface while continuing your digital transformation.

Pyry Grönholm
CEO
Email: pyry.gronholm@prosysopc.com
